Exploring the 2026 Evolution of EV Software Security: Protecting Your Vehicle from Cyber Threats
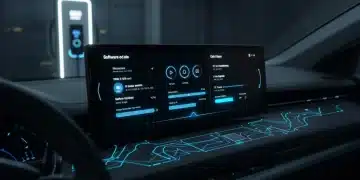
The automotive industry is undergoing a monumental transformation, driven by the rapid adoption of Electric Vehicles (EVs). As we approach 2026, the discussion around EV software security has never been more critical. Modern EVs are essentially computers on wheels, packed with sophisticated software that controls everything from battery management and propulsion to infotainment and autonomous driving features. This intricate web of code, while enabling groundbreaking functionalities, also introduces a new frontier for cyber threats. Understanding and mitigating these risks is paramount to ensuring the safety, privacy, and reliability of our electric future.
In this comprehensive article, we will delve deep into the evolving landscape of EV software security in 2026. We’ll explore the types of cyber threats that electric vehicles face, the current state of security measures, and the projected advancements and challenges that lie ahead. Our goal is to provide a clear picture for EV owners, manufacturers, and enthusiasts alike on how to protect these technologically advanced machines from malicious attacks.
The Rise of Software-Defined Vehicles: A Double-Edged Sword for EV Software Security
The term ‘software-defined vehicle’ is becoming increasingly commonplace, and for good reason. Unlike traditional cars, EVs rely heavily on software for their core operations. This software enables over-the-air (OTA) updates, allowing for continuous improvements, new features, and critical security patches. However, this connectivity and reliance on code also expand the attack surface for potential cybercriminals. Every line of code, every connected sensor, and every communication protocol represents a potential vulnerability that could be exploited.
Connectivity as a Vulnerability Vector
EVs are inherently connected. They communicate with charging stations, cloud services, other vehicles (V2V), and infrastructure (V2I). This constant data exchange, while beneficial for navigation, traffic management, and remote diagnostics, also creates numerous entry points for cyberattacks. A compromised charging station, for instance, could potentially introduce malware into a vehicle’s system. Similarly, vulnerabilities in cloud-based services used by EV manufacturers could expose sensitive user data or even allow remote vehicle control.
The Expanding Attack Surface in 2026
By 2026, the complexity of EV software systems will have grown significantly. We anticipate more advanced autonomous driving capabilities, increased integration with smart home ecosystems, and even more sophisticated infotainment systems. Each new feature, while enhancing the user experience, often adds layers of code and new communication channels, inherently increasing the potential for security gaps. Therefore, robust EV software security strategies must evolve in parallel with these technological advancements.
Understanding the Cyber Threats to EV Software Security
To effectively protect electric vehicles, it’s crucial to understand the diverse range of cyber threats they face. These threats can range from nuisance hacks to potentially life-threatening attacks that compromise vehicle safety systems.
Remote Exploits and Malicious Code Injection
One of the most concerning threats is the ability of attackers to remotely exploit vulnerabilities in an EV’s software. This could involve injecting malicious code through unpatched software, compromised network connections, or even through the vehicle’s infotainment system. Successful remote exploits could lead to:
- Unauthorized Vehicle Control: Imagine an attacker gaining control of your steering, braking, or acceleration. While highly sophisticated, this is a theoretical risk that manufacturers are actively working to prevent.
- Data Theft: Personal data, driving habits, location history, and even financial information linked to charging payments could be stolen.
- System Disruption: Attackers could disable critical vehicle functions, rendering the EV inoperable or severely limited.
Supply Chain Attacks
The software components in an EV often come from numerous suppliers. A vulnerability introduced at any point in this complex supply chain – from a third-party software library to a hardware component with embedded firmware – could compromise the entire vehicle. Manufacturers must maintain rigorous security audits and validation processes for all components, a challenge that will only intensify by 2026.
Charging Infrastructure Vulnerabilities
As mentioned, charging stations represent a potential attack vector. Unsecured charging points could be used to inject malware into an EV’s battery management system (BMS) or other critical components. Furthermore, the data exchanged during charging, such as payment information and battery health diagnostics, must be securely encrypted to prevent eavesdropping or manipulation. Ensuring the security of the entire charging ecosystem is integral to comprehensive EV software security.
Privacy Breaches and Data Exploitation
EVs collect a vast amount of data about their users and their environment. While this data is valuable for improving vehicle performance and developing new services, it also presents a significant privacy risk. Without robust encryption and strict data governance, this information could be accessed by unauthorized parties, leading to privacy breaches or even identity theft. By 2026, regulatory frameworks like GDPR and CCPA will likely have even stronger implications for how EV manufacturers handle user data.
Current and Evolving Security Measures for EV Software Security in 2026
Automotive manufacturers and cybersecurity experts are not standing still. Significant investments are being made to develop and implement robust security measures to counter these threats. By 2026, we expect to see even more sophisticated approaches becoming standard.
Secure Over-the-Air (OTA) Updates
OTA updates are a double-edged sword. While they offer convenience and rapid deployment of fixes, they also represent a crucial attack vector if not properly secured. In 2026, secure OTA updates will be non-negotiable. This involves:
- Cryptographic Signing: Ensuring that all updates are digitally signed by the manufacturer to verify their authenticity and prevent tampering.
- Encrypted Transmission: Protecting update packages during transit to prevent interception and modification.
- Secure Boot Mechanisms: Ensuring that only legitimate, signed software can be loaded and executed by the vehicle’s ECUs (Electronic Control Units).
Intrusion Detection and Prevention Systems (IDPS)
Just like in enterprise networks, IDPS are becoming essential for EVs. These systems monitor vehicle networks for suspicious activity, such as unusual data flows or unauthorized access attempts. By 2026, AI and machine learning will play a larger role in IDPS, enabling them to detect novel threats and adapt to evolving attack patterns in real-time. An effective IDPS is a cornerstone of proactive EV software security.
Hardware Security Modules (HSMs) and Secure Elements
Hardware-based security is a critical layer of defense. HSMs and secure elements are dedicated hardware components designed to perform cryptographic operations and securely store sensitive data, such as encryption keys. These components are highly resistant to tampering and provide a root of trust for the entire system, making it incredibly difficult for attackers to compromise core vehicle functions.
Robust Network Segmentation
Modern EVs have multiple internal networks (e.g., CAN bus, Ethernet). Segmenting these networks and implementing strict access controls between them can limit the damage of a successful breach. For example, isolating the infotainment system from critical safety systems ensures that a compromise on the former doesn’t affect the latter. This architectural approach is fundamental to resilient EV software security.
Threat Modeling and Penetration Testing
Before an EV even hits the market, rigorous threat modeling and penetration testing are crucial. This involves systematically identifying potential vulnerabilities and attempting to exploit them in a controlled environment. By 2026, these practices will be continuous, with manufacturers constantly testing their software against the latest attack techniques and collaborating with white-hat hackers to uncover weaknesses.
The Role of Regulations and Standards in EV Software Security
Recognizing the growing importance of automotive cybersecurity, regulatory bodies worldwide are stepping up. By 2026, these regulations will have a profound impact on how EVs are designed, manufactured, and maintained.
UN R155 and R156 Regulations
The United Nations Economic Commission for Europe (UNECE) has introduced two pivotal regulations: R155 (Cybersecurity and Cyber Security Management System) and R156 (Software Update and Software Update Management System). These regulations mandate that vehicle manufacturers implement a cybersecurity management system (CSMS) across the entire vehicle lifecycle and ensure the security of software updates. Compliance with these standards is becoming a prerequisite for selling vehicles in many international markets, significantly bolstering EV software security.
ISO/SAE 21434 and Other Industry Standards
Beyond government regulations, industry standards like ISO/SAE 21434 (Road vehicles – Cybersecurity engineering) provide a framework for automotive manufacturers and suppliers to manage cybersecurity risks throughout the product development process. Adherence to such standards helps in building security into the design from the ground up, rather than attempting to patch vulnerabilities retrospectively. These standards are continuously evolving to address new threats, making them vital for maintaining robust EV software security.
Challenges and Future Outlook for EV Software Security in 2026
Despite significant progress, several challenges remain in the quest for impregnable EV software security. The dynamic nature of cyber threats means that the battle for security is never truly won; it’s an ongoing process of adaptation and innovation.
The Skills Gap in Automotive Cybersecurity
One of the most pressing challenges is the shortage of skilled cybersecurity professionals with expertise in automotive systems. The unique blend of embedded systems, real-time operating systems, and network protocols found in EVs requires specialized knowledge. Bridging this skills gap through education and training programs will be crucial for the industry’s ability to develop and maintain secure vehicles.
Legacy Systems and Integration Complexities
Even as new EVs are designed with security in mind, the sheer number of existing vehicles with varying levels of security features presents a challenge. Integrating new security technologies with older architectures can be complex and costly. Furthermore, the long lifespan of vehicles means that security patches and updates must be supported for many years, demanding a sustained commitment from manufacturers.
The Evolution of Artificial Intelligence in Security
By 2026, AI will not only be a feature within EVs (e.g., for autonomous driving) but also a powerful tool in both offensive and defensive cybersecurity. AI-powered threat detection systems will become more sophisticated, capable of identifying subtle anomalies that indicate an attack. However, attackers may also leverage AI to develop more potent and evasive malware. This arms race between AI security and AI-powered attacks will define a significant aspect of future EV software security.
Consumer Awareness and Best Practices
Ultimately, the human element remains a critical factor. EV owners play a role in their vehicle’s security. By 2026, manufacturers and regulators will need to do more to educate consumers on best practices, such as:
- Keeping Software Updated: Promptly installing OTA updates when they become available.
- Using Strong Passwords: For connected apps and services.
- Being Wary of Public Wi-Fi: Limiting connections to unsecured public networks.
- Reporting Suspicious Activity: Notifying manufacturers of any unusual vehicle behavior.
Increased consumer awareness will form a vital layer in the overall defense strategy for EV software security.
The Economic and Societal Impact of EV Software Security
The implications of robust EV software security extend far beyond individual vehicle owners. A major cyberattack on a fleet of EVs or critical charging infrastructure could have significant economic and societal repercussions.
Economic Stability and Trust
Consumer trust is fragile. A widespread security breach could severely damage the reputation of EV manufacturers and erode public confidence in electric vehicle technology as a whole. This could slow down EV adoption, impacting climate goals and economic growth in the automotive sector. Conversely, a strong track record of security builds trust and accelerates market penetration.
National Security Implications
As EVs become more integrated into smart city infrastructure and potentially even military applications, their cybersecurity becomes a matter of national security. Attacks could disrupt transportation networks, compromise critical infrastructure, or even be used for espionage. Governments are increasingly recognizing this and collaborating with the industry to establish resilient security frameworks for EV software security.
Insurance and Liability
The legal and insurance landscapes are also evolving to address cybersecurity risks in EVs. Determining liability in the event of a cyberattack that causes damage or injury is a complex issue. Robust security measures can help mitigate these risks, potentially leading to lower insurance premiums and clearer legal frameworks for both manufacturers and owners.
Conclusion: A Secure Future for Electric Mobility
As we look towards 2026, the evolution of EV software security is a continuous journey, not a destination. The increasing sophistication of electric vehicles demands an equally sophisticated approach to cybersecurity. Manufacturers, regulators, cybersecurity experts, and even consumers all have a vital role to play in building a secure electric future.
By embracing advanced security technologies, adhering to stringent regulations, fostering collaboration across the industry, and educating users, we can collectively work to protect electric vehicles from the ever-present threat of cyberattacks. The promise of sustainable, connected, and autonomous mobility hinges on our ability to ensure that the software powering these vehicles is as resilient and secure as the hardware itself. The focus on proactive, layered security will ensure that the exciting advancements in EV technology can be enjoyed safely and confidently for years to come.